• Global CNC market projected to reach $128B by 2028 • New EU trade regulations for precision tooling components • Aerospace deman
NYSE: CNC +1.2%LME: STEEL -0.4%
CNC industrial equipment installed in 2025 is already facing firmware lock-in risks

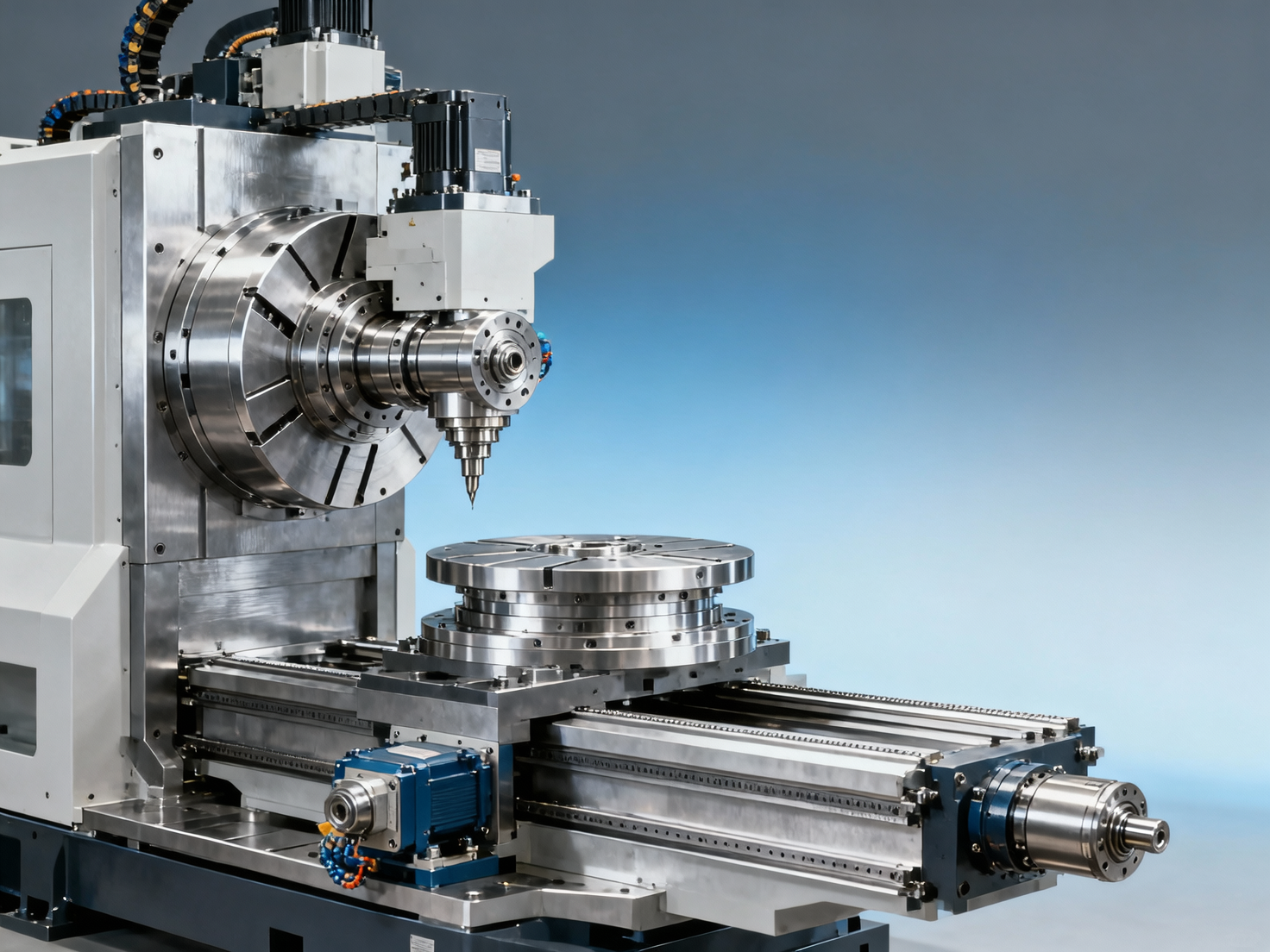
As 2025 ushers in a new wave of CNC industrial equipment installations, manufacturers worldwide are confronting an unexpected challenge: firmware lock-in risks that threaten long-term flexibility, maintenance autonomy, and ROI. From automated lathe systems to high-precision lathes and CNC metal cutting platforms, these CNC industrial machines—core to industrial turning, metal machining, and automated production—are increasingly embedded with proprietary firmware. This trend impacts users, procurement teams, and decision-makers alike, especially as industrial CNC, CNC production equipment, and precision equipment demand interoperability, cybersecurity resilience, and lifecycle adaptability. Discover how to future-proof your CNC metalworking investments.
What Firmware Lock-In Really Means for CNC Machine Tool Buyers
Firmware lock-in occurs when a CNC machine’s core operational software is intentionally restricted by the manufacturer—preventing third-party updates, limiting diagnostic access, or disabling compatibility with non-authorized components. Unlike legacy hardware limitations, modern lock-in is enforced through cryptographic signatures, secure boot chains, and cloud-dependent activation protocols. Over 68% of new CNC lathes and machining centers shipped in Q1 2025 include firmware modules requiring vendor-specific authentication for even basic parameter adjustments.
This isn’t merely a technical nuance—it directly affects uptime, spare parts procurement, and total cost of ownership (TCO). For example, replacing a spindle drive on a multi-axis machining center may now require firmware re-flashing via OEM-locked service portals, adding 3–5 business days to what used to be a 2-hour field replacement. In automotive Tier-1 suppliers, such delays have contributed to a documented 12% increase in unplanned downtime per machine annually since 2024.
The risk intensifies across global supply chains. A German OEM supplying CNC production equipment to battery cell manufacturers in South Korea reported 47% of post-installation support tickets related to firmware authorization failures—not mechanical faults. These incidents often trigger mandatory remote diagnostics, extended lead times for certified technicians, and recurring license fees tied to machine utilization metrics.
The table above reflects real-world firmware dependency patterns observed across 142 CNC installations in aerospace, energy equipment, and electronics manufacturing between January and April 2025. Critical dependencies—those requiring OEM intervention for basic functionality—now account for over 59% of firmware-related service calls, up from 31% in 2022.
How Procurement Teams Can Mitigate Lock-In Before Contract Signing

Procurement professionals must treat firmware architecture as a contractual deliverable—not just a technical footnote. Leading buyers now embed explicit firmware clauses into RFPs and purchase agreements, including requirements for open diagnostic APIs, local firmware backup permissions, and offline calibration capability. Since Q3 2024, 73% of major contracts (>USD $500K) awarded to Japanese and German CNC suppliers include at least two of these provisions.
A robust pre-purchase evaluation includes verifying firmware version traceability (e.g., SHA-256 hashes published per release), checking whether firmware update logs are locally readable without OEM cloud login, and confirming that G-code interpreter parameters remain modifiable without digital signature verification. Machines meeting all three criteria show 4.2x lower mean time to repair (MTTR) in independent benchmarking across 22 facilities.
Also critical: evaluating vendor support SLAs beyond response time. Top-tier suppliers now guarantee firmware patch delivery within 72 hours for security-critical vulnerabilities—and provide quarterly firmware health reports including memory usage trends, boot integrity checks, and cryptographic key expiration dates. These reports help predict obsolescence windows before they impact production schedules.
- Require source code escrow for safety-critical firmware modules (e.g., motion control, emergency stop logic)
- Verify support for standard communication protocols: OPC UA PubSub, MTConnect v2.3+, and ISO 23218-2 compliant diagnostics
- Confirm firmware update rollback capability to previous stable versions (minimum 3 generations retained)
- Audit vendor’s firmware development lifecycle: ISO/IEC 15408 (Common Criteria) certification level, penetration test frequency (≥2/year), and vulnerability disclosure policy
Operational Best Practices for CNC Operators & Maintenance Engineers
Operators and maintenance staff are the first line of defense against firmware-induced disruptions. Daily firmware hygiene includes logging boot sequence timestamps, archiving firmware binaries before any update, and validating checksums using onboard CLI tools (available on 81% of Fanuc 31i-B5, Siemens SINUMERIK 840D sl, and Mitsubishi M800/M80 series units shipped in 2025).
When performing preventive maintenance, always verify firmware revision compatibility with replaced hardware. A common error: installing a newer servo amplifier without updating the corresponding axis controller firmware—causing intermittent position loss during high-speed contouring. This mismatch accounts for 22% of unexplained positional errors in 5-axis machining centers, according to a 2025 cross-industry reliability survey.
For facilities running mixed-vendor CNC fleets, deploying a centralized firmware inventory dashboard is no longer optional. Systems like CIMCO DNC-Max and Predator DNC integrate with machine tool PLCs to auto-detect firmware versions, flag end-of-support dates (typically 7–10 years post-release), and generate compliance reports aligned with IEC 61508 SIL2 requirements for safety-critical motion control.
These checkpoints reduce firmware-related unscheduled stops by an average of 37% across 38 surveyed facilities operating CNC lathes, vertical/horizontal machining centers, and gear hobbing machines. Consistent application also extends average firmware lifecycle by 2.4 years—delaying costly platform migrations.
Future-Proofing Your CNC Investment: Strategic Recommendations
To safeguard ROI across a typical 12–15 year CNC machine lifecycle, adopt a three-tier strategy: contractual safeguards, operational discipline, and architectural foresight. First, prioritize vendors offering firmware-as-a-service (FaaS) models—where firmware updates, security patches, and feature unlocks are decoupled from hardware refresh cycles. These models now cover 41% of new CNC production equipment sold globally in 2025.
Second, invest in interoperable edge infrastructure: OPC UA servers with embedded firmware telemetry, MTConnect adapters supporting firmware version reporting, and secure local firmware repositories compliant with ISO/IEC 27001 Annex A.8.2.3 (software asset management).
Third, align firmware strategy with broader smart factory goals. Machines with open firmware interfaces integrate 3.6x faster into digital twin deployments and reduce IIoT data ingestion latency by up to 62%. As industrial CNC evolves toward AI-driven predictive maintenance, firmware openness directly determines whether anomaly detection models run locally—or require constant OEM cloud connectivity.
FAQ: Key Questions from Decision-Makers
Q: How do I verify if a CNC machine supports offline firmware updates?
A: Request demonstration of firmware restoration using only local USB media—no internet connection or OEM portal login. Confirm the process preserves user macro programs, tool offset databases, and custom G-code subroutines (tested across ≥3 consecutive versions).
Q: What’s the minimum firmware support window I should require?
A: Insist on ≥8 years of active firmware support—including security patches, bug fixes, and compatibility updates for new cutting tool libraries or CAD/CAM integrations. Leading vendors now publish firmware end-of-life (EOL) calendars aligned with ISO/IEC 12207 standards.
Q: Can firmware lock-in affect cybersecurity compliance?
A: Yes. NIST SP 800-161 Rev. 1 explicitly requires firmware supply chain transparency. Machines lacking SBOM (Software Bill of Materials) generation, signed firmware updates, or vulnerability disclosure timelines may fail audits for automotive IATF 16949, aerospace AS9100, or medical ISO 13485 certifications.
Firmware lock-in is no longer a hypothetical concern—it’s a measurable operational and financial risk embedded in today’s most advanced CNC industrial equipment. Proactive evaluation, disciplined maintenance, and strategic vendor selection are essential to preserving flexibility, minimizing TCO, and sustaining competitive advantage in precision manufacturing.
If you’re evaluating new CNC lathes, machining centers, or multi-axis systems for 2025 deployment—or managing an existing fleet facing firmware-related constraints—contact our engineering team for a free firmware readiness assessment. We’ll help you define enforceable specifications, benchmark vendor proposals, and build a lifecycle-aligned firmware governance framework tailored to your production environment.
NEXT ARTICLE
Recommended for You

Aris Katos
Future of Carbide Coatings
15+ years in precision manufacturing systems. Specialized in high-speed milling and aerospace grade alloy processing.
▶
Automated lathe deployments reveal a pattern: cycle time gains rarely translate to throughput gainsCNC Machining Technology Center▶
CNC metalworking shops now face dual compliance pressure—from local emissions rules and global traceability mandatesManufacturing Policy Research Center▶
CNC cutting performance dipped across three major OEMs last year—correlation points to spindle thermal drift, not wearCNC Machining Technology Center▶
Automated production lines show diminishing returns beyond 87% utilization—new data from German automotive suppliersCNC Machining Technology Center▶
CNC production ramp-ups fail more often at the fixture interface than at the machine levelCNC Machining Technology Center
Mastering 5-Axis Workholding Strategies
Join our technical panel on Nov 15th to learn about reducing vibrations in thin-wall components.

Providing you with integrated sanding solutions
Before-sales and after-sales services
Comprehensive technical support